EdgeURL MCP Server
Connect any Model Context Protocol-aware AI agent (Claude Desktop, Claude.ai, ChatGPT, Cursor, Continue) to your EdgeURL identity. Spec-compliant OAuth 2.1 + PKCE + RFC 8707, agent-driven signup with magic-link confirmation, Ed25519-signed action receipts (verifiable offline), and out-of-band approval channels for the writes that matter.
Three ways to connect
The same server speaks both transports. Pick whichever your client supports:
- Claude.ai Custom Connector (Pro / Max / Team / Enterprise) -- add a remote connector pointing at
https://mcp.edgeurl.io/api/mcp. Claude handles OAuth automatically. - Claude Desktop / Cursor / Continue / any stdio client -- install our npm wrapper
@edgeurl/mcpand let it stdio-bridge to the remote server. - ChatGPT custom GPT -- add
https://mcp.edgeurl.io/api/mcpas an action; OAuth metadata is auto-discovered.
Quick verify (no auth needed)
Confirm the server is reachable and inspect its tool surface in 5 seconds:
npx @modelcontextprotocol/inspector https://mcp.edgeurl.io/api/mcp
Discovery endpoints
- /.well-known/oauth-authorization-server— RFC 8414 OAuth metadata
- /.well-known/oauth-protected-resource— RFC 9728 Protected Resource Metadata
- /.well-known/mcp— EdgeURL manifest + receipt verifier public key
14 tools live
Tools with scope: public require no user auth. Capability-scoped tools require a Bearer mcp_at_* token from the OAuth flow. Mutating tools require Idempotency-Key.
| Tool | Scope | What |
|---|---|---|
| lookup_profile | public | Schema.org Person JSON-LD for any EdgeURL username |
| search_creators | public | Discover index search by query / category / profile_type |
| verified_socials | public | Social accounts the profile owner has proven they control (returns platform_url per row) |
| signup_user | public + client-auth | Initiate agent-driven signup; magic-link to claimed_email |
| check_signup_status | public + client-auth | Poll signup status; returns access_token on confirm (one-shot) |
| list_links | link.read | Paginated list of org links; each row enriched with short_url |
| create_link | link.create | Create a short link; SSRF-safe URL validator; Idempotency-Key required |
| update_link | link.update | Update target_url or is_active; tenant-scoped; Idempotency-Key required |
| delete_link | link.delete | Delete a link; destructiveHint:true; Idempotency-Key required |
| get_profile | profile.read | Read own bio profile; returns profile_url + edit_url |
| update_profile | profile.update | Update title, bio, discover categories; Idempotency-Key required |
| query_analytics | analytics.read | Aggregate click count for a period; retention-clamped per plan |
| account_info | account.read | Effective plan, limits, current usage, dashboard shortcuts |
| bridge_delegate | bridge.delegate | Forward a tool call to another MCP server (Stripe, Linear, GitHub) |
Clickable URLs in every result
Every tool that returns user-owned data also embeds the canonical public URL for that data so AI clients render clickable links inline:
get_profile—profile_url,edit_urlupdate_profile—profile_url,edit_urllist_links— each link getsshort_urlupdate_link/delete_link—short_urlin dry-run + commit responseverified_socials—profile_url+ per-rowplatform_urlaccount_info—shortcutsblock (dashboard, billing, settings, AI agents, pricing)query_analytics—analytics_dashboard_url
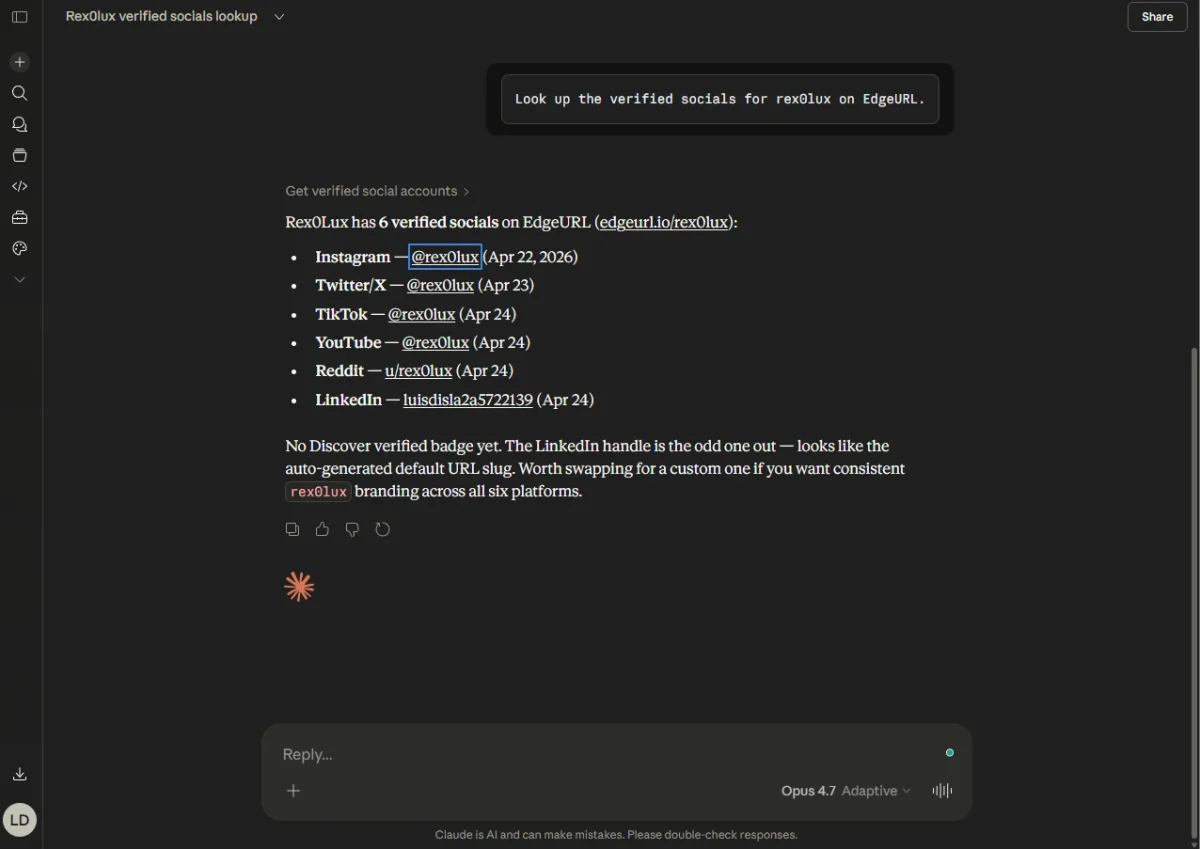
verified_socials returned a per-row platform_url plus a top-level profile_url, and Claude rendered them as inline links. Click @rex0lux next to Twitter/X and you land on x.com; click edgeurl.io/rex0lux and you land on the bio.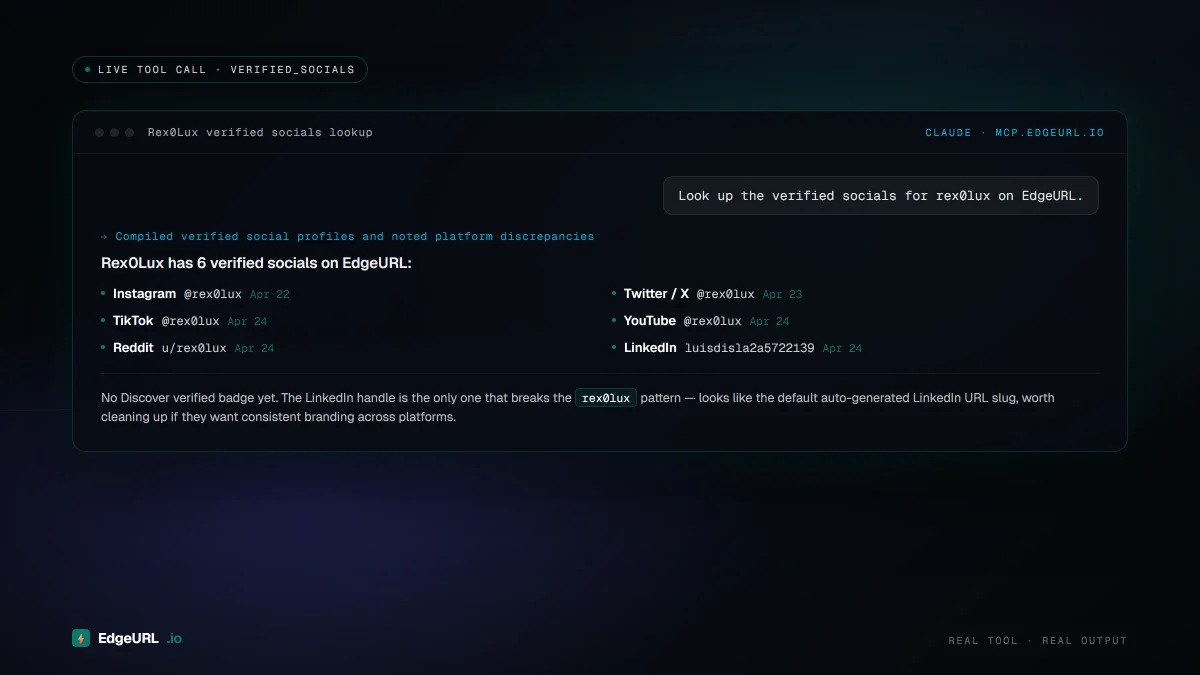
Connect Claude Desktop
Drop this into claude_desktop_config.json:
{
"mcpServers": {
"edgeurl": {
"command": "npx",
"args": ["-y", "@edgeurl/mcp"],
"env": { "EDGEURL_API_KEY": "<your_mcp_at_token>" }
}
}
}The @edgeurl/mcp wrapper is published on npmjs.com. It is a thin stdio-to-HTTPS proxy with no business logic -- all tools, OAuth, receipts, and approvals live on the remote server, so the wrapper never needs an upgrade for new tools.
Connect Claude.ai web
In Claude.ai (Pro / Max / Team / Enterprise), open Settings → Connectors → Add custom connector, paste https://mcp.edgeurl.io/api/mcp, and approve. Claude walks through the OAuth handshake itself; you only see the standard "this app would like access to..." consent screen with the requested scopes.
Connect ChatGPT
ChatGPT desktop and web both support remote MCP servers via Streamable HTTP. Add a custom connector pointing at https://mcp.edgeurl.io/api/mcp -- ChatGPT will OAuth-handshake automatically using the discovery metadata above. For a Custom GPT, point its action endpoint at the same URL with OAuth as the auth scheme.
OAuth scope vocabulary
During the OAuth flow, the agent requests one or more scopes. The user sees them on the consent screen and either approves the full set or declines. Scopes are least-privilege -- never grant more than the agent's role requires.
| Scope | What it allows |
|---|---|
| link.read | Read your short links |
| link.create | Create new short links |
| link.update | Update target / status of links you own |
| link.delete | Permanently delete links you own (destructive) |
| profile.read | Read your bio profile |
| profile.update | Update your bio (title, bio text, categories) |
| analytics.read | Aggregate click counts (retention-clamped per plan) |
| account.read | Read your plan, limits, and usage counters |
| bridge.delegate | Forward calls through EdgeURL to another MCP server |
Agent-driven signup
Two-step ceremony. The agent calls signup_user(claimed_email) with its registered X-MCP-Client-Id header. EdgeURL emails the user a magic link. The user confirms in their own browser at /agent-signup/[token], sees the exact scopes the agent will receive, and approves. The agent polls check_signup_status(poll_id) and receives the scoped access token (one-shot retrieval).
This is the only path on the public internet that lets a brand-new user create an account from chat without ever typing a password into the assistant. The email owner is always the gate.
Signed action receipts
Every successful authenticated tool call writes an Ed25519-signed JWS receipt to mcp_action_receipts. Receipts are hash-chained per user (prev_receipt_hash = sha256(prev.signed_payload)) and verifiable offline against the public key at /.well-known/mcp. Default private; users toggle visibility per-receipt.
Public receipt: GET https://mcp.edgeurl.io/api/mcp/receipts/[id]
Verify offline (Node):
import { jwtVerify, importJWK } from 'jose'
const meta = await fetch('https://mcp.edgeurl.io/.well-known/mcp').then(r => r.json())
const pub = await importJWK(meta.receipt_verifier_jwk, 'EdDSA')
const receipt = await fetch('https://mcp.edgeurl.io/api/mcp/receipts/<id>').then(r => r.json())
const { payload } = await jwtVerify(receipt.signed_payload, pub, { algorithms: ['EdDSA'] })
console.log('Verified action:', payload)Out-of-band approval channels
Configure per-action-class rules: in-app push, SMS, Telegram bot, email, webhook. Mutating tool calls return -32100 pending_approval with a poll URL; the agent retries with X-MCP-Approval-Id header after the user approves on whatever channel they chose.
Manage your channels at /dashboard/settings/ai-agents.
Cross-MCP bridge
The bridge_delegate tool lets an agent on Claude or ChatGPT forward a tool call to another MCP server (Stripe, Linear, GitHub) using EdgeURL as the trusted token broker. List integrations being onboarded:
GET https://mcp.edgeurl.io/api/mcp/bridge
See the launch blog for the full architecture story, the npm package on npmjs.com, or jump back to /docs.